Fleet Manager, an easy way to check in on an EC2 Windows instance
Want to learn more about AWS Lambda and .NET? Check out my A Cloud Guru course on ASP.NET Web API and Lambda.
I’ve been using EC2 Windows instances for a while and from time to time I want to check in on something, this usually involves opening up the RDP port in the security group, connecting, then reverting the security group change. Not too much trouble, but some security teams don’t like changes like that being made. If you don’t know how to setup an EC2 instance check out this post.
Fleet manager offers an alternative, a quick way to connect without requiring changes to the security group.
But you do need to add a security policy to the IAM role the instance is running under.
If you don’t know how to setup a Windows instance check this post.
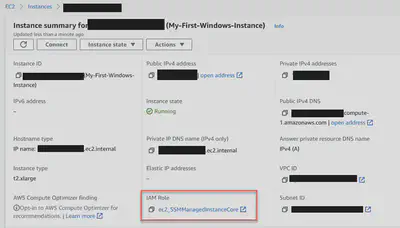
If you already have an instance running, it will look something like this -
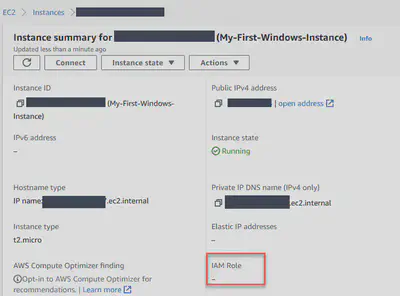
Note how the IAM Role is blank in this example. Yours may be like this, or it may have a role.
For Fleet Manager to work you need an IAM Role assigned to the instance, and the role must have the AmazonSSMManagedInstanceCore policy attached.
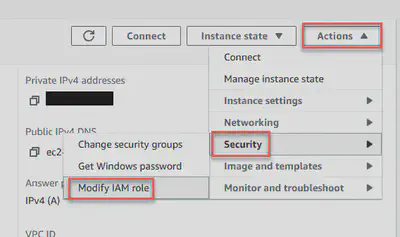
Attaching the role
As mentioned above, your instance may or may not have an IAM role attached. Either way, the fix is the same, go to “Actions”, then “Security”, then “Modify IAM role”.
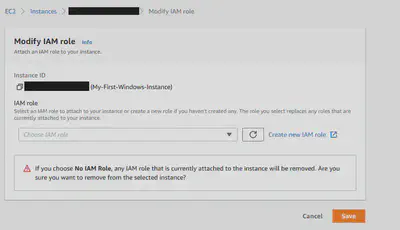
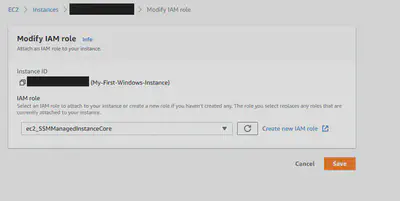
You will see a screen like the one below, where the IAM role is blank. Click on “Create new IAM role”. (If there is an IAM role here already, you can modify that role instead of creating a new one.)
On the next page, click “Create role”.
This will bring you to a page with a variety of options, select EC2 near the top and hit “Next: Permissions”.

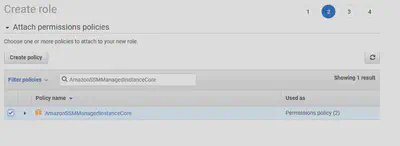
On the next page, you will add the policy needed to Fleet Manager to work, filter the list with “AmazonSSMManagedInstanceCore”, select that policy by ticking the box on the left. Hit “Next: Tags”.
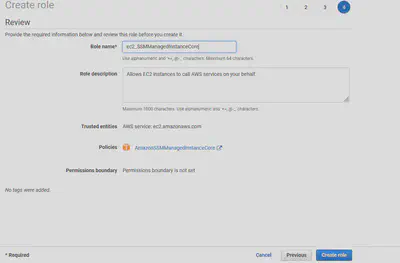
You can skip adding a tag, hit “Next: Review”. Now you’ll be on the review page, give the role a name, and hit “Crete role”.
Go back to the page where you were modifying the IAM role for the instance you are working on and select this new role from the dropdown list, you may need to hit the little reload icon to the right of the list. Hit “Save”.
You will now be back at the instance summary page, the IAM Role should now show the role you just attached.
Even though you can see the role on the instance, it may take some more time before you can connect to the instance from Fleet Manager. In my experience, it usually happens within 10 minutes.
Connecting from the Fleet Manager
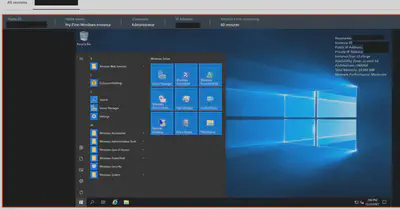
Head over to the Fleet Manager, and you should see something like the below. If you don’t, wait a few minutes more minutes and try again.

Click on the “Node ID”, then on the new page, click Node Actions, and “Connect to With Remote Desktop”.

Finally, you need to authenticate yourself, you can use the key pair you generated when you created the instance, or another form of authentication like active directory credentials, or local machine credentials.
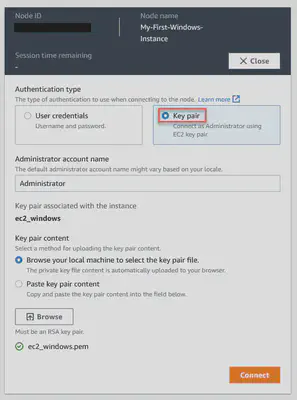
And then you will connect!